Updated December 14 in light of the recent APT 29 supply chain attack.
The recent and unfolding news about the Russian APT 29, or Cozy Bear, SolarWinds breach is a sobering reminder of the relentlessness of nation-state cyber attack campaigns, which have turned their attention to vulnerabilities created by supply chain backdoors. You can read more about Cozy Bear's techniques in our Russia threat report.
While companies across sectors have been shoring up their cybersecurity defenses with technologies such as firewalls, endpoint protection, and Network Detection and Response, these recent events call for renewed vigilance for securing the supply chain.
Indirect attacks into the supply chain now account for 40 percent of security breaches, according to the Accenture Security / Third State of Cyber Resilience Report. Indeed, the days of having well-defined data boundaries are gone, and traditional data protections are no longer sufficient to secure these ecosystems.
How can you protect your supply chain from data breaches, including intellectual property theft, while recognizing that many of the companies that work in the supply chain have neither the revenue nor the capacity to really run an in-house Security Operations Center?
As IronNet’s Co-CEO General (Ret.) Keith Alexander recently discussed with Sandy Carter, VP, Amazon Web Services, during a Carahsoft webinar on the federal supply chain, "What companies are now looking at is securing the supply chain: Getting an umbrella over the thousands of companies in the defense supply chain to help secure them is part of our future. We have got to do it.”
We’re no longer talking about just a physical supply chain of moving a product from production to market. Today’s supply chain is an extended, connected web that spreads in every direction. It can be a digital supply chain where risks such as compromised code present a third-party risk (as recently revealed in a malicious iOS SDK used in 1,200 apps downloaded in total about 300 million times a month).
In its “Meeting the Requirements of the Supply Chain Imperative," white paper, the government IT solutions provider Carahsoft reported that across the federal IT supply chain last year, for example, CISA identified nine threat groups, including counterfeit parts and insider threats.
“As IT supply chains grow more complicated, they also become more vulnerable. Much like a physical chain has physical links, IT supply chains contain interrelated parts that can become prey for bad actors.”
Securing the weak spots in your supply chain
While an individual company may have hundreds, even thousands of third-party entities, across its supply chain, it’s important to keep in mind that a single company’s brand and reputation are on the line. Supply chain vendors often remain behind the scenes, yet they can inadvertently open the so-called back door through which large-scale supply chain attacks are launched.
Clearly it’s time to scrutinize third-party risk with vigilance. Where are the weak spots?
5 common types of supply chain attacks
Sophisticated attackers know where the weak spots are, and they are taking advantage of these backdoor ways to infiltrate a company’s ecosystem. Here are some techniques they are using to attack:
- Business Email Compromise (BEC): Often associated with financial transfers, where criminals leverage the fact that business is often conducted via email.
 Using vulnerability information gleaned from OSINT tools: Finding weaknesses in supplier or vendors in your supply chain to exploit in order to gain entry to your networks.
Using vulnerability information gleaned from OSINT tools: Finding weaknesses in supplier or vendors in your supply chain to exploit in order to gain entry to your networks.- “Living off the land” (or “fileless”) attacks: Gaining additional access using tools that already exist in the computing environment.
- Embedded systems: Accessing backdoors through network-aware embedded systems, Operational Technology (OT), and IoT devices.
- Service providers: Taking advantage of the potential risk associated with the usage of third-party service providers.
How to defend against these attacks
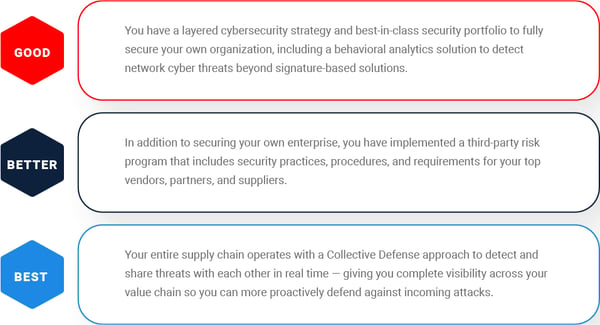
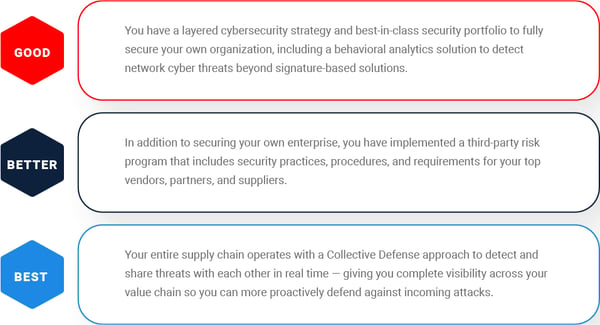
The question is how to detect and defend against these attacks. We recommend the following Good, Better, Best scenarios:
In response to these recent events, we have removed the registration page from our supply chain white paper. Learn about the 6 most common supply chain entry points for cyber attacks, and the 5 most common attacks and how to defend against them.


.png)