On May 4th, Cybereason released a report on a malicious cyberattack campaign by the Chinese state-sponsored APT, Winnti group. The campaign, dubbed Operation CuckooBees, has been targeting technology and manufacturing companies in North America, Western Europe, and East Asia since at least 2019. Using both known and previously undocumented malware techniques, including digitally signed kernel-level rootkits, Winnti managed to go undetected for years.

At IronNet, we look to behavioral analytics to detect unknown threats on enterprise networks before adversaries succeed at their endgame: exploitation or exfiltration. First, we do the threat detection groundwork needed to spot abnormal network activity across our customers’ networks. Second, our IronDefense NDR expert system scores these alerts, prioritizing the most interesting events to help cut down on alert fatigue. Finally, we take a Collective Defense approach to crowdsourced threat intelligence exchange in real time.
The June IronNet Threat Intelligence Brief
This ability to analyze and correlate seemingly unrelated instances is critical for identifying sophisticated attackers who leverage varying infrastructures to hide their activity from existing cyber defenses. As reported in the June Threat Intelligence Brief, our analysts review alerts from millions of data flows that are ingested and processed with big data analytics. We apply ratings to the alerts (benign/suspicious/malicious) and immediately share them with IronDome Collective Defense participants.
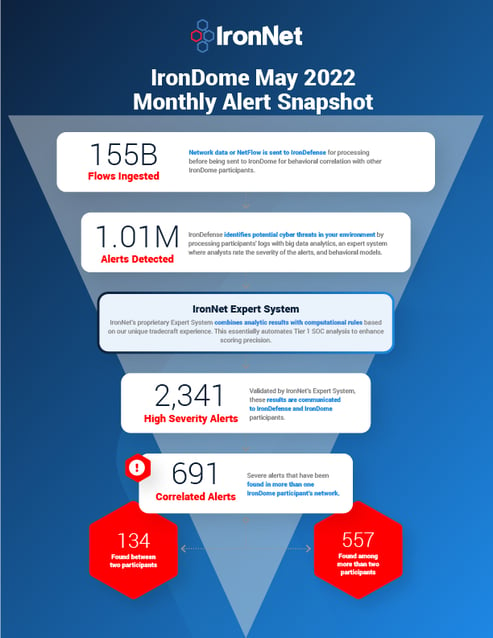
Here is a snapshot of what we discovered across the IronDome communities in May, showing 691 correlated alerts across IronDome participant environments:
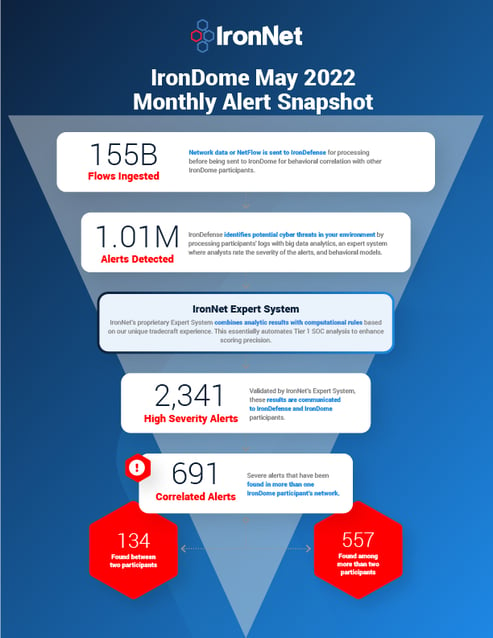
Given the unique cross-sector visibility and Collective Defense capabilities of IronDome, we are able to highlight the most frequent behaviors each month, in turn enabling us to track trends over time. For May, the most frequent behavior analytics were DNS Tunneling (125), New and Suspicious Domains (66), and Credential Phishing (60).
Analysis of IOCs
In addition to correlated alerts, significant IronDome community findings revealed 643 Indicators of Compromise (IOC) that may pose risk to IronDome participant environments. For example, we analyzed the malicious domain 2kmovie[.]cc, which was created in 2020 and hosts new movies for download, but has hosted malicious files in the past, therefore we recommend analyzing traffic and blocking the domain.
All the IOCs we analyzed are used to trigger alerts that are mapped to the Cyber Kill Chain to identify the stage and progression of the threat. They can be used to create detection rules for network, endpoint, or other security tools currently deployed to mitigate cyber risk in each IronDome participant’s environment.
See the June Threat Intelligence Brief for the full list of recent IOCs.
The bigger picture of Collective Defense
Every month, IronNet’s expert threat analysts create threat intelligence rules (TIR) based on significant community findings from IronDome, malware analysis, threat research, or other methods to ensure timely detection of malicious behavior targeting an enterprise or other IronDome community participants.
In May, we created 2,315 threat intel rules of our 307,029 created to date. Some examples of this month’s research related to indicators associated with malware delivery domains for Cobalt Strike, BUMBLEBEE, and Emotet malware.
This combination of behavior-driven and IOC signature-based detection, alert ranking, and sharing ensures IronDome participants have the broadest view of threats facing their enterprise.
Operation CuckooBees
In the attacks, the threat actors employed an elaborate, multi-stage infection chain that was critical to enabling the group to remain undetected for so long. In this, the threat actors implemented a delicate “house of cards” approach, meaning that each component depends on the others to function properly, thus making it very difficult for researchers to analyze each component separately. The researchers were able to uncover previously undocumented malware strain called DEPLOYLOG as well as new versions of known Winnti malware, including Spyder Loader, PRIVATELOG, and WINNKIT. All of these malwares or payloads play a distinct role in the multi-staged infection chain, where each phase relies on the previous one in order to execute correctly, and the whole thing is only successful upon the complete deployment of all of the payloads.
You can see the latest industry news in the full brief or check out IronNet’s threat intelligence hub.


.png)